“the price of data freedom is eternal vigilance”1
2017 started with a bang for the cyber security threat outlook.
On January 2, Donald Trump told reporters at a function in Florida when asked a question about alleged Russian hacking;
“…If you have something really important, write it out and have it delivered by courier, the old fashioned way, because I’ll tell you what, no computer is safe. I don’t care what they say, I’m telling you, no computer is safe…”2
Was Trump right? Is it really that bad? Was Trump exaggerating? Have hacking and ransomware become the ‘new normal’? Is the cyber threat only relevant for governments and large corporations? (answers: yes, yes, no3, yes, and no).
Security vendor Trend Micro has released a number of key reports analysing cyber threat incidents in 2016 and 2017, with some alarming facts4:
- 2016 was an unprecedented year for cybersecuritythreats, particularly for enterprises.
- ransomware spiked 752% in 2016.
- Email is the #1 infection vector for malware. Spamremained the top ransomware vector, accounting for 79% of attacks. These spam emails contain malware-infected attachments and URL links.
- Business email compromise (BEC) is a major source of breaches, yielding huge profits for cybercriminals.
You may think that hackers and cyber criminals won’t really be interested in the data from a small medical practice. Think again:
“The healthcare sector has been the industry with the highest number of data breaches, followed by the government and retail sectors…”5
In the report, The Next Tier; Trend Micro Security Predictions for 2017, cyber criminals are predicted to ’double up’ on profit taking:
“…ransomware will become an increasingly commonplace component of data breaches. Cybercriminals will first steal confidential data to sell in underground markets, then install ransomware to hold data servers hostage, doubling their profit.”6
Security vendor Webroot also confirms the bad news on ransomware, with Hal Lonas, Chief Technical Officer, commenting that, “we can see how ransomware is rewriting all the rules”, and “the bad guys used to want your data because it was valuable to them. If [they] could get your credit card number or your identity or a secret from your company, [they] could go sell that.” When asked what makes ransomware different, Lonas said: “The interesting thing about ransomware is that criminals are now saying, ‘Your data is valuable not to me, the bad guy, but to you. How much is your data worth to you?’
They’re betting that you don’t have any backup and protection in place, so their angle is to take your data and hold it for ransom until you decide what the value is, and then you pay them.”… 7
Australian healthcare organisations are already aware of regulatory and compliance requirements. These requirements will increase with the passage of the Privacy Amendment (Notifiable Data Breaches) Bill 2016 on 13 February 2017 by the Senate, with the new provisions expected to come into force in 2018 (or earlier if by proclamation)8
With these very real risks to data security and the increasing burden of responsibility placed on practice principals, directors and practice managers,9 what can you do to mitigate the risks?
The Office of the Australian Information Commissioner (OAIC) website10, has a number of excellent resources, including the Guide to securing personal information; ‘Reasonable Steps’ to protect personal information.11 Compare your data security practices against the ‘reasonable steps’ described here by the OAIC, because the OAIC will refer to this guide in data breach investigations.
Readers may also recall a Newsbites item from The Practice Manager, Issue 1, 201712 where email account users were warned by the Prime Minister’s Special Advisor on Cyber Security, Mr Alastair MacGibbon, ”on reducing the likelihood of these things impacting them, like changing their passwords and using two-factor identification on any service.” I have previously described security risk mitigation strategies in earlier articles of The Practice Manager13, 14, 15, 16
Practice managers and principals would be well advised to follow at a minimum the following three key data defence strategies:
1. Backup, Backup, Backup – the 3-2-1 Rule
I can’t reiterate often enough the importance of data backup and indeed complete system backup. Note again Lomas’ comments above that cyber criminals are, … “betting that you don’t have any backup and protection in place, so their angle is to take your data and hold it for ransom until you decide what the value is, and then you pay them.
”Of course the backup is only as useful as it can be readily and fully restored.
No ‘restorability’ = No backup!
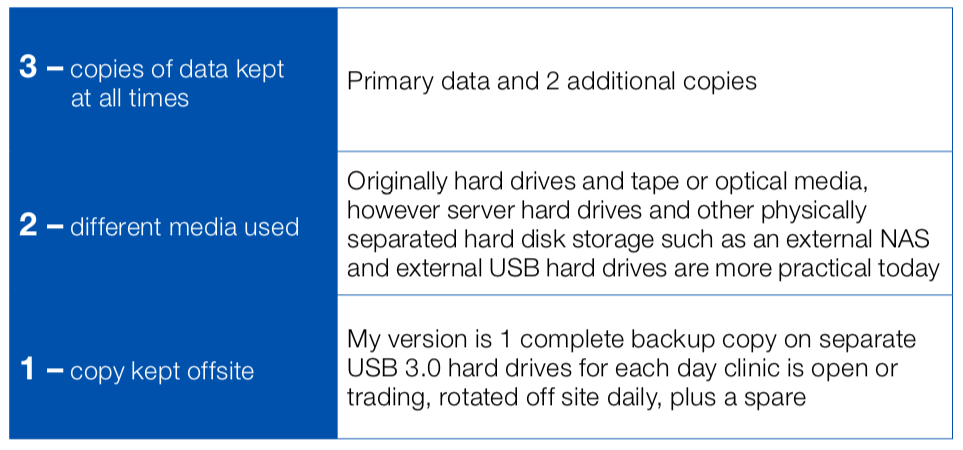
A simple but still very effective backup strategy for data backup is to follow the 3-2-1 rule.17, 18 This should be the minimum backup strategy for medical practice data (and system configuration). Here is my simplified version of the 3-2-1 rule:
2. Layered /Combination Security
Trend Micro warns, “The [threat] actors will come up with new targeted attack tactics that circumvent current anti-evasion solutions” and summarises the best defence strategies;19

Figure 1: USB 3.0 hard drives for off-site backup
“This challenge calls for a combination (versus a silver-bullet type approach) of different security technologies that should be available across the network to form a connected threat defense. Technologies like:
- Advanced anti-malware (beyond blacklisting);
- Antispam and anti-phishing at the Web and messaging gateways; • Web reputation;
- Breach detection systems;
- Application control (whitelisting);
- Content filtering;
- Vulnerability shielding;
- Mobile app reputation;
- Host- and network-based intrusion prevention; and
- Host-based firewall protection.
3. Continuous cyber security awareness training for all computer users
As the majority of security breaches are due to careless or compromising actions by users on the inside of a network, staff training is the third key strategy, particularly educating users to be continually alert to threats from emails, social media and targeted attacks.
Trump unfortunately was right; “…no computer is safe”. Please, please ensure you are following ‘reasonable steps’ in cyber security as the consequences for not doing so could be horrendous for your practice…
References
- en.wikiquote.org/wiki/Thomas_Jefferson#Attributed,accessed July 2016, my ‘update’
- www.smh.com.au/video/video-news/video-world-news/trump-no-computer-is-safe-20170102-4oz8m.html, accessed April 2017.
- The assumption here is, if your computer is turned on and is connected to the internet, it is inherently unsafe.
- www.trendmicro.de/cloud-content/us/pdfs/security-intelligence/reports/rpt-the-next-tier.pdf, accessed April 2017
- www.trendmicro.com/content/dam/trendmicro/en/security-intelligence/research/reports/wp-cybercrime-&-other-threats-faced-by-the-healthcare-industry.pdf, accessed April 2017
- Ibid, www.trendmicro.de/cloud-content/us/pdfs/security-intelligence/reports/rpt-the-next-tier.pdf
- www.webroot.com/blog/2016/12/21/ransomware-stops-clients/, accessed April 2017
- www.oaic.gov.au/media-and-speeches/statements/mandatory-data-breach-notification, accessed April 2017
- ‘Defence Mechanism’, by Domini Stuart, ‘Company Director’ magazine, AICD, July 2016, pp40-45
- www.oaic.gov.au/, accessed April 2017
- www.oaic.gov.au/agencies-and-organisations/guides/guide-to-securing-personal-information, accessed April 2017
- The Practice Manager, Issue 1, 2017, page 4
- ‘Practice IT Security 2013, Part 1’, The Practice Manager, Issue 2, 2013, page 8
- ‘IT Security 2013 – Part 2’, The Practice Manager, Issue 3, 2013, page 16
- ‘Practice IT Security 2014 Update’, The Practice Manager, Issue 3, 2014, page 26
- ‘Practice IT Security Update 2016’, The Practice Manager, issue 3, 2016, page 20
- Peter Krogh, ‘The DAM Book: Digital Asset Management for Photographers’, 2ND Edition, O’Reilly Media, 2009, page 207
- Peter Krogh summarises 3-2-1 Backup in this article: www.dpbestflow.org/backup/backup-overview#321, accessed April 2017
- www.trendmicro.com.au/vinfo/au/security/research-and-analysis/predictions/2017, accessed April 2017
